c0c0n 2022 talk | Maximizing ROI on cyber security investments: Do you think Adversary Simulation OR Purple teaming holds the key? | 27 Sep 2022
My thoughts and slides from the talk delivered at c0c0n conference on the topic, Maximizing return of investments on cyber security investments and significance of adversary simulation slash Purple teaming
About c0c0n Conference
c0c0n is a 15 years old platform that is aimed at providing opportunities to showcase, educate, understand and spread awareness on Information Security, data protection, and privacy. It also aims to provide a hand-shaking platform for various Corporate, Government organizations including the various investigation agencies, academia, research organizations, industry leaders and players, for better coordination in making the cyber world a better and safe place to be. Various technical, non-technical, legal and community events as part of the conferences. c0c0n website: https://india.c0c0n.org/2022/
Here is the abstract of the talk.
Organizations are governed by demands of the market and other external stakeholders, primarily regulatory bodies. To deliver services to the market/consumer faced organizations are required to maintain the highly complex infrastructure that scales periodically, targeted Cyber threats faced by organizations too are highly complex and sophisticated in nature. In order to keep pace with threat landscape and enhance the defenses against such threats, organizations are required invest in new generation of security products and services. Ransomware campaigns and state sponsored cyber threat actors are mutate quickly to evolving defense mechanisms, thereby forcing organizations and financial institutions to invest more and more towards Cyber Security. How does an organization evaluate the ROI corresponding to the investment? How does an organization make an unbiased assessment on it’s current maturity level to evaluate whether or not the investment has helped them achieve a higher maturity in terms of security posture.
This talk will give the audience an insight into Adversary simulation, purple teaming, Breach and attack simulation and other offensive security powered operations; which would ultimately help you to assess the security defense posture of your organization. The talk will explore how threat Intel torqued threat actor or ransomware simulation/APT simulation could uncover the effectiveness of your cyber defense capabilities in terms of people, process and technology. The talk will also look into maximizing the potential/value of security investments such as SOC, Endpoint security tools (EDR, AV, EPM, DLP, Proxies), MDR, IT and security staff, Firewalls/WAF etc; by assessing how well are they configured and evaluate the response readiness to threats.
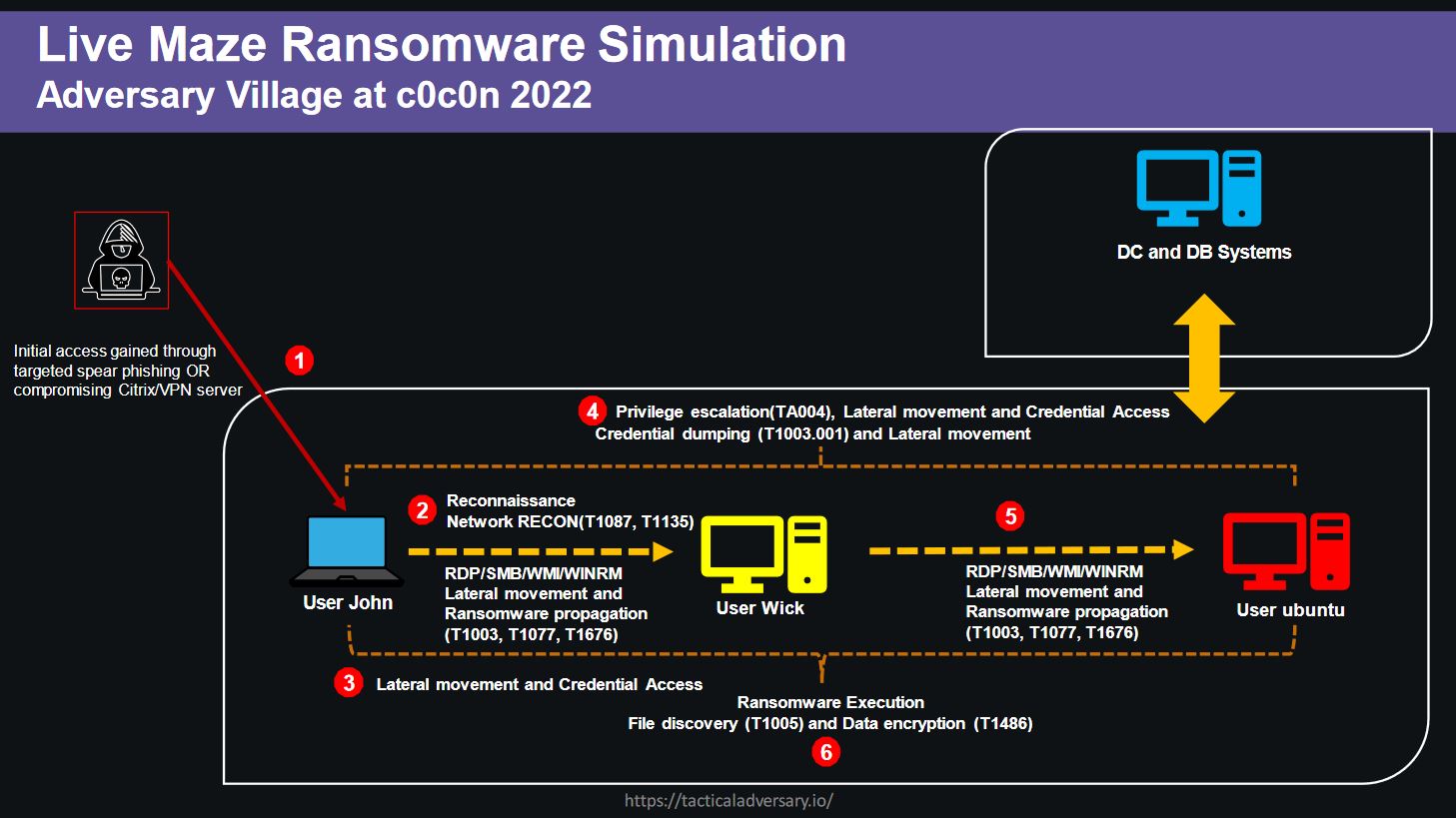
As part of the c0c0n conference I also have organized Adversary Village with a handful of hands-on activities. A live ransomeware emulation exercise for the participants using caldera was one of the highlights. Attaching below, Maze ransomware emulation plan diagram which I had created for the hands-on ransomware emulation exercises.