MITRE ATT&CK® Defender Adversary Emulation Methodology Certification Review | 11 November 2022

Backstory
Certifications and writing certification reviews are not really my thing. This might be my first time writing a training and certification review. A while ago, I had the opportunity to go through the MITRE ATT&CK Defender (MAD) training program. It focuses on a niche but highly captivating area within the cyber security industry.
About MITRE ATT&CK DEFENDER™ (MAD)
To quote MITRE Engenuity website;
MITRE ATT&CK Defender™ (MAD) is a training and credentialing program for cybersecurity operations and individuals looking to strengthen their threat-informed defense approach to security. Through a mix of on-demand and live training opportunities that focus on certifying real-world mastery in the application of the MITRE ATT&CK® knowledge base, MAD helps organizations stay ahead of adversaries.
MAD's program is centered around imparting real-world skills that can be readily applied to operational settings. Through courses, assessments, and an agile credentialing program, MAD emphasizes skills training and practical expertise. As a result, certified defenders can promptly integrate and utilize the ATT&CK knowledge base in their work environment, making an immediate impact on their operations.
The course covers the following areas;
- ATT&CK for Cyber Threat Intelligence (CTI)
- ATT&CK for Security Operations Center (SOC) Assessments
- ATT&CK for Adversary Emulation Methodology
- ATT&CK for Threat Hunting and Detection Engineering
- ATT&CK Purple Teaming Fundamentals
For this blog entry I'll be focusing only on the Adversary Emulation methodology module.
ATT&CK Adversary Emulation Methodology Certification
The Adversary Emulation training modules enhances a practitioner's ability to carry out adversary emulation engagements based on real-world threats. The MA'Defender slash participant gains knowledge and demonstrates expertise in researching, implementing, and executing adversary tactics, techniques, and procedures (TTPs). This proficiency of operators helps organizations in evaluating and enhancing their cyber security defense systems. More details on the training can be found here in this URL: https://mitre-engenuity.org/cybersecurity/mad/mad-curriculum/ Following are the modules covered as part of the training program.
Module 0: ATT&CK® Fundamentals
ATT&CK Fundamentals is the first piece of the MITRE ATT&CK Defender training series. This module does a detailed introduction to the MITRE ATT&CK framework, Structure, TTPs, Threat-Informed Defense etc. and it was created by Jamie Williams, a good friend of mine.
Module 1: ATT&CK Adversary Emulation Fundamentals
This introductory module provides an overview of the course content, objectives, and the significance of adversary emulation. Simply highlights the importance of understanding how threat actors operate and how red team operations play a vital role in assessing an organization's defensive capabilities. We could gain an understanding of the different stages of an adversary emulation engagement, from planning to execution. This module introduces adversary emulation framework, which serves as a structured approach for emulating real-world cyber threats. Talks about the tactics, techniques, and procedures (TTPs) employed by adversaries during attacks. Gives us an overview about setting realistic goals, determining success criteria, and aligning the engagement objectives with the organization's overall cyber security strategy.
What is Adversary Emulation?
Here is a solid explanation of the term 'adversary emulation', as mentioned in this module.
Adversary Emulation is an intelligence driven discipline that entails researching, modeling, and executing cyber adversary tactics, techniques and sub-techniques, and procedures (TTPs) to assess and improve cybersecurity.
Lab Sessions:
There is a walkthrough of the Center for Threat-Informed Defense (CTID) adversary emulation library, an open and free repository that facilitates the replication of real adversary tactics and techniques. Detailed guidance included on setting up your own lab environment and Executing FIN6 Adversary emulation plan with the help of Metasploit. One more thing to point out is that a subscribed users would get access to the Cyber Ranges cloud hosted lab environment to carry out the lab exercises.
Module 2: Researching Adversary TTPs
In this module, we get an overview of various aspects of threat emulation, starting with researching cyber threats to gain critical insights, learn how to strategically select the specific threat to emulate, followed by selecting the appropriate Tactics, Techniques, and Procedures (TTPs) to replicate.
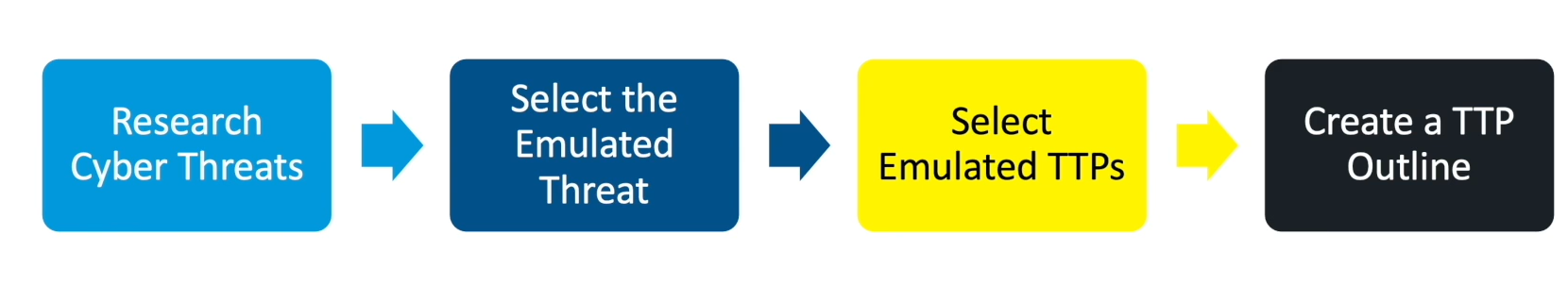
As the module progresses, we could learn more about constructing a meticulous TTP outline, ensuring a realistic and accurate emulation of threat actor behavior. Additionally, the module will focus on addressing intelligence gaps to ensure a thorough understanding of potential vulnerabilities.
Module 3: Adversary Emulation Planning
This module provides insights on how to plan adversary emulation engagements effectively. It guides the participants slash operators through the process of planning and emphasizes its importance in ensuring professionalism and safety during adversary emulation activities. The module underscores the importance of planning for maintaining professionalism and safety during adversary emulation activities. It outlines key components such as objectives, scope, schedule, rules of engagement, permissions, and communication plans. The adversary emulation planning template is a helpful resource to drive planning activities. It assists network slash business owners step by step through the adversary emulation planning process, offering guidance on defining scope, establishing rules of engagement, and approving authorities. This template and other resources are available on the MAD GitHub repository: https://github.com/maddev-engenuity/AdversaryEmulation/tree/main/resources
Module 4: Adversary Emulation TTP Implementation
This module explains the essence of TTP implementation, outlines the prerequisites required for effective execution, and emphasizes the importance of establishing a robust lab environment. What is TTP Implementation, describes about the procedure of executing one or more adversary behaviors. TTP implementation section include all procedures and resources necessary to execute adversary bahaviors. It encompasses all the necessary resources required for successful TTP execution. Importantly, it acknowledges that TTP implementation doesn't follow a rigid format, as various projects may have their distinct conventions.
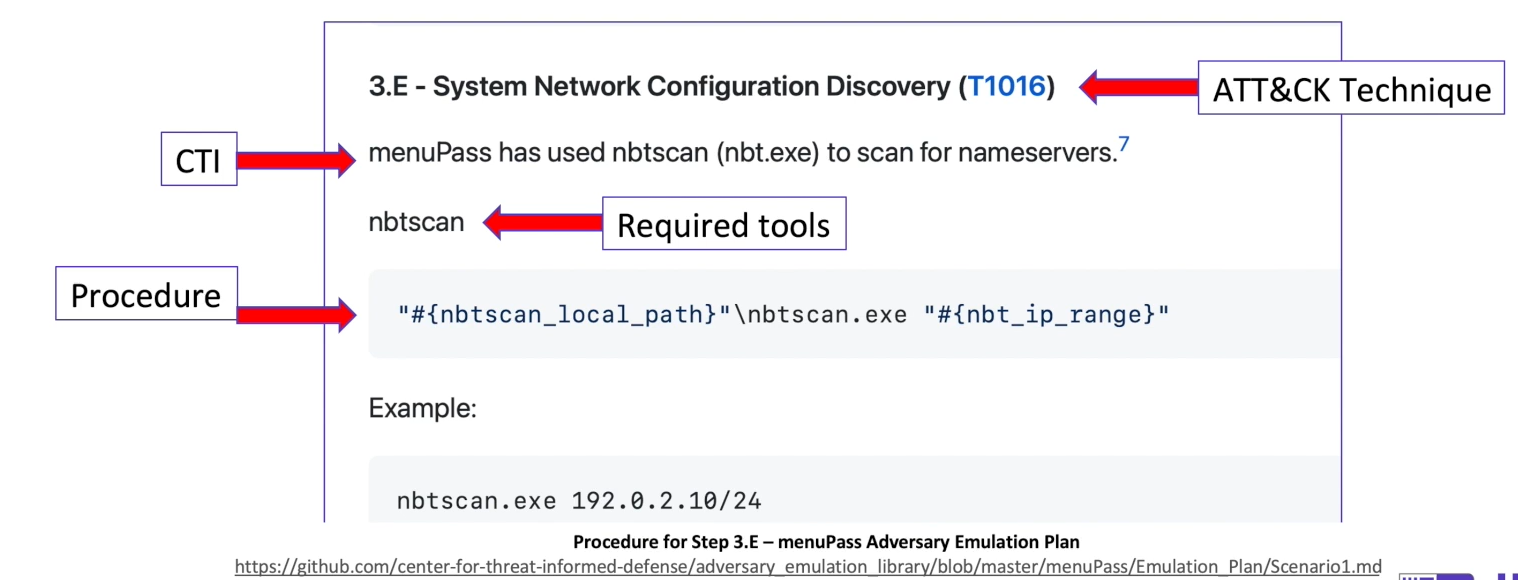
Also gives is an overview of the structured process of TTP implementation. It comprises several stages, starting with planning the implementation, followed by the execution of TTPs, automation possibilities, and the integration of outcomes into an adversary emulation plan.
Lab Sessions:
The lab sessions in this module includes detailed hands-on activities on, Implementing adversary TTPs (Utilize ATT&CK to understand APT29 targets and TTPs, Create an initial access payload based on APT29 CTI etc.), Automating adversary TTPs, Identifying Detections and Mitigations etc.
Module 5: ATT&CK Adversary Emulation Execution
This module covers the following components in general: Review your TTP Implementation, Execute the TTPs, Observe Results, Document and Report Findings. Additionally, it addresses the topic of Dealing with Unexpected Situations like Responding to Error / Failure Conditions, Broken systems and Unprofessionalism. A significant part of this section is about documenting Adversary Emulation Activities which includes Operations notes, Engagement Report, and engaging presentation materials.
Lab Sessions:
The final lab module elaborates on Developing an Adversary Emulation Plan from scratch. Helps the participant to Develop a post-compromise emulation plan for a threat actor relevant to the organization. It has everything, starting from researchng relevant threat actors to actual commands to execute. Threat actor selection, Developed attack path, Convert technique list to emulation plan etc. have walkthroughs in detail in this module. Spoiler alert! The lab guide and other resources can be downloded free from CTID GitHub repository. Lab guide: Lab 5.1 Developing an Adversary Emulation Plan.pdf Full repository: https://github.com/maddev-engenuity/AdversaryEmulation
Certification Badges earned
Each module has a small exam which will let you earn badges. I liked it, It was pretty cool. We get to show-off the badges and my earned badges for each learning module with timeline is shown below.

Note-taking MAD'ness
We are in the age of information overload. Taking notes in the traditional way does not work all the time. I'm a big fan of Obsidian! I have tried many other systems in the past. But now, most of my technical notes, cheatsheets and other stuff are kept in Obsidian and Joplin. Here is a GIF of my notes captured only for the Adversary Emulation training.
MAD Hoodie!
Who doesn't like hoodies? As part of the #PurpleTeamingMonth promotions, the training team sent hoodies to all subscribers. I also received a nice FREE hoodie!

How to enroll MAD training?
I appreciate this training initiative by MITRE Center for Threat-Informed Defense [CTID]. Should you be interested in giving it a shot, there are two choices: a paid subscription and a free training option. Paid subscription comes with a certification program and lab access via Cyber Ranges. Cyber Ranges also offers a community lab access for this course. The second option lets you learn for FREE of cost, which is amazing considering the effort they have put into building this focused training program. You would be supporting MITRE ATT&CK Defender program to continue providing freely available educational content, if you opt for the paid subscription. Totally up to you!